Digital forensics is growing while being more tied with incident response, according to the latest State of Enterprise Digital Forensics and Incident Response survey from Magnet Forensics. However, some digital forensics professionals are burned out and need more automation and leadership in the DFIR field, where hiring is difficult.
This survey from Magnet Forensics, which develops digital investigation solutions, was conducted between October and November 2022.
Jump to:
Digital forensics increasingly involved with incident response
Digital forensics, sometimes called computer forensics, has been an expertise domain that was mostly deployed on single computers for many years. The typical use cases were to find data on an employee’s computer who was suspected of committing an offense, or investigating legal or malware issues such as information stealers.
Over time, attacks have grown in complexity and size and target several computers or servers from companies, often at the same time. Digital forensics, which was all about analyzing full hard drive copies in an offline mode, saw a twist when it became necessary to analyze running systems.
As a result, digital forensics found new ways to integrate that complexity with incident response teams. It allowed more deep-dive analysis on systems while not shutting them down, and now digital forensics and incident response are usually together in the SecOps team within the Security Operations Center.
Targeted attacks are typically the case where digital forensics works ideally with incident response. While incident response works on containing, resolving and recovering from an incident, digital forensics might be the best solution to find the root cause of an incident.
The learnings from every incident response and digital forensics actions help companies find the weak spots in their defenses and implement new safeguards and processes.
Most common DFIR incidents
According to Magnet Forensics, data exfiltration or IP theft represents 35% of the overall activity and is the most common DFIR incident, followed closely by business email compromise (Figure A). Fourteen percent of the survey respondents indicated that their organization encounters BEC scams very frequently. Other common incidents are employee misconduct, misuse of assets or policy violations, internal fraud and ransomware-infected endpoints.
Figure A
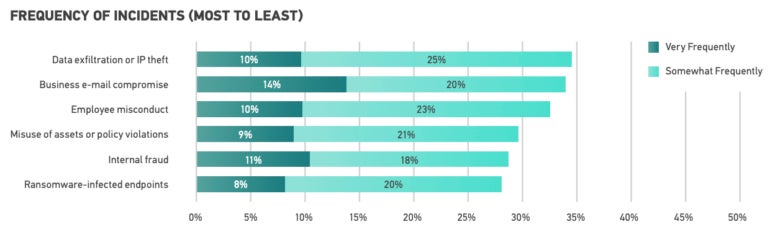
Data exfiltration, IP theft and ransomware have a huge impact on organizations. DFIR professionals have a hard time working on it, because experience and equipment are necessary to rapidly investigate ransomware and data breach incidents, while cybercriminals try to render those investigations as difficult as possible.
The challenges of evolving cyberattack techniques
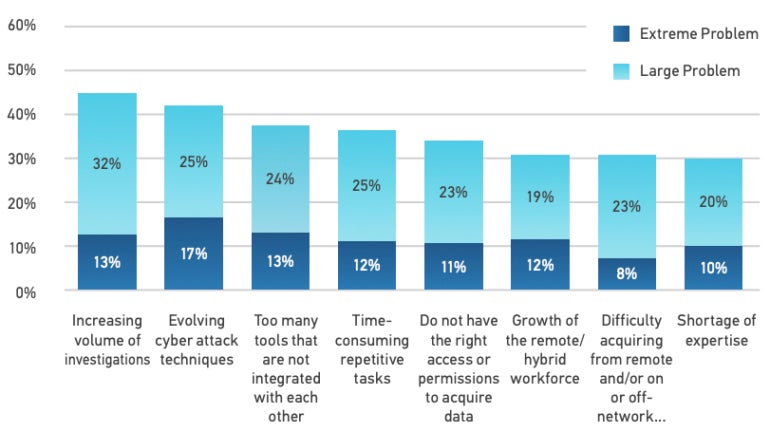
Attacks are evolving in size and complexity, with threat actors using more techniques to make detection harder; as a result, 42% of DFIR professionals indicate evolving cyberattack techniques present either an extreme or large problem in their organization.
Staying up to date about such cyberattacks is a challenge, with companies relying more on R&D specialists focusing on equipping the organization with new and ever-evolving tactics, techniques and procedures. Great sources of information regarding evolving threats include MITRE, CISA, and LinkedIn or Twitter accounts of cybersecurity researchers.
More automation for DFIR is needed
A lot of repetitive tasks need to be done in DFIR, and tools automating those tasks are often needed.
SOCs already make use of automation as much as possible, as they need to deal with telemetry, but automation for digital forensics is different, as it mostly needs data processing by orchestrating, performing and monitoring forensic workflows.
Half of DFIR professionals indicate that investments in automation would be greatly valuable for a range of DFIR functions, as workflows still rely too much upon the manual execution of many repetitive tasks.
More than 20% of the survey respondents indicated automation would be mostly valuable for the remote acquisition of target endpoints, the triage of target endpoints, and processing of digital evidence, as well as documenting, summarizing and reporting on incidents.
The survey respondents indicated that the growing volume of investigations and data is either an extreme (13%) or large (32%) problem (Figure B).
Figure B
DFIR personnel challenges
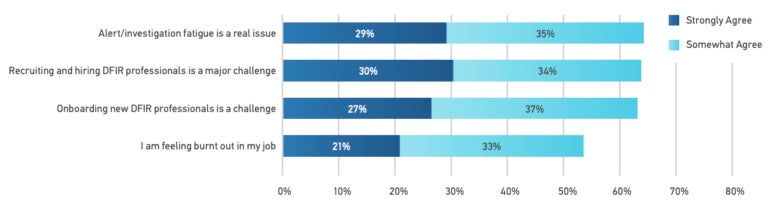
Nearly 30% of corporate DFIR practitioners agree that investigation fatigue is a real issue, while 21% strongly agree that they feel burnt out in their jobs. The volume of investigations and data, and the stress caused by the necessity of running incident responses fast, makes it difficult for those professionals to relax. Automation might help save these professionals time and enable faster analysis.
Recruitment is indicated as a major challenge by 30% of the survey respondents, while onboarding new DFIR professionals can also be difficult because the job might vary a lot based on the company; for instance, this could impact the tools used (Figure C).
Figure C
More DFIR leadership is needed to help with data and regulations
A field under such rapid evolution needs informed and decisive leadership to set strategies and direct resources in an efficient way. Leaders influence the way DFIR professionals can efficiently access data sources they need, which is often difficult, as more than a third of the survey respondents indicated.
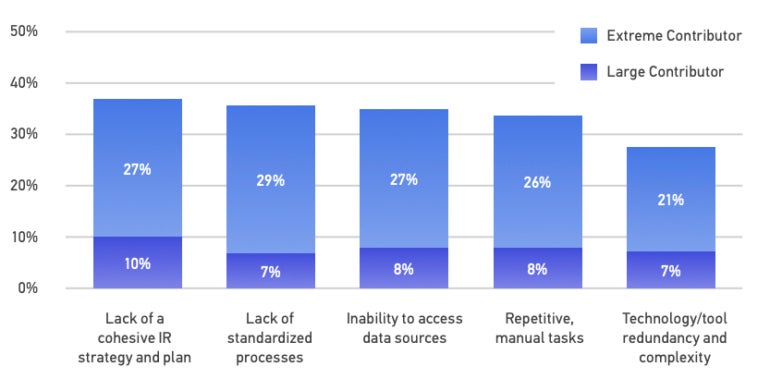
The biggest contributions to wasted resources are the lack of a cohesive incident response strategy and plan and the lack of standardized processes (Figure D).
Figure D
Regulations are another challenge for DFIR professionals. For instance, 67% of DFIR professionals indicated that their role has been impacted by new reporting regulations, and 46% of the respondents reported not having enough time to fully understand new and changing legislation. Leaders need to understand regulations and decide how to handle them, perhaps by freeing up DFIR teams’ time to study the regulations or consulting with the company’s legal department.
Outsourcing with DFIR investigations is common
Most companies generally outsource parts of their DFIR investigations, mostly because there is a lack of those skills internally. Almost half of the respondents (47%) indicate the lack of expertise as the prior reason for using service providers, while the second reason (38%) cited is not having the required toolset, which might be extremely expensive in some cases.
DFIR recommendations for businesses
Companies should invest in DFIR solutions that prioritize speed, accuracy and completeness. More delays means more risk when it comes to analyzing incidents.
Automation should be strongly enforced to help DFIR professionals reduce burnout and reduce investigation delays.
An incident response plan is essential. The plan will clarify roles and responsibilities and detail how forensics and incident response needs to be done. It should also help accessing data with clear directives and indications as to who provides what in the company. Critical positions to provide access to data should be reachable 24/7.
Regulations and legislations need to be fully understood by DFIR teams. More generally, everything that could be done in advance to prepare for future incidents should be carefully thought of and done when not working on an incident.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.
Read next: Security Incident Response Policy (TechRepublic Premium)
Source of Article