Ernie Anderson, Chief U.S. Services Officer of Kudelski Security, was interviewed by Safety Detectives’ Aviva Zacks. She got a chance to ask him about his fascinating journey to cybersecurity.
Safety Detectives: What was your journey to cybersecurity?
Ernie Anderson: I wish I could say that I predicted cybersecurity would be a hot topic when I started my professional career almost 20 years ago, but I just got lucky in choosing my career path. I grew up with technology and computers in the house, having a mother who worked for IBM for over 25 years before retiring. I always knew that I wanted to be in IT and enable businesses to work smarter, faster, and be more connected. Coming out of school at the peak of the dot com era was both exciting and scary. It was exciting because the Internet was connecting people in new ways never thought of before and technology advances were happening in leaps and bounds. It was a scary time because the business models behind companies advancing IT were breaking new ground. This translates into a lot of change and uncertainty, which included getting laid off from my first “real job” due to a restructuring effort shortly after joining so the business could try to reposition for the emerging economy.
After that, I spent about a year searching for systems administrator jobs and found myself moving across the country from Boston to San Diego. By searching random job boards, I found work at a management consulting firm looking for a system/security administrator to manage all the hardware and software in their web application development environment. The role I filled grew out of a public breach that stemmed from non-security focused developers’ insecurely managed systems, including opening unnecessary firewall ports, deploying misconfigured systems, and a slew of general hygiene matters that would make any of today’s security professionals shake their head. My primary goal was to maintain security configurations of systems and monitor the lab. The funny thing about that job was I learned the most about hardening systems by figuring out how our developers were trying to circumnavigate controls because they didn’t have access to what they needed and doing things they weren’t supposed to. Fast forward 20 years, I’m still in the cybersecurity industry and just as excited about it as when I was a twenty-something out of college.
SD: What is Kudelski Security’s flagship product or service?
EA: Kudelski Security is an innovative, independent provider of cybersecurity solutions for large companies and public sector clients. We support our clients in the development, deployment, and administration of cybersecurity solutions through a combination of advanced managed security services, consulting, and security technologies.
As a managed security services provider (MSSP), we have invested millions of dollars into our experts, our methodologies, and infrastructure. We have honed our capabilities to separate the signal from the noise through our 24x7x365 Cyber Fusion Center (CFC), which provides management of all security devices across all environments – on-prem, cloud, OT, and IIoT. It also fuses contextualized threat intelligence with human analysis of data to rapidly identify, contain, and mitigate threats. We apply the information we gather from one network or system to every network or system we monitor, making our intelligence richer and more complete. For most organizations, the kind of investment such coverage would require makes no business sense.
SD: What industries use your solutions?
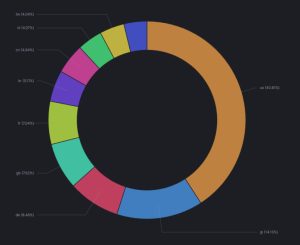
EA: Our clients include Fortune 500 enterprises and government organizations in Europe and across the United States. Key industries that use Kudelski Security’s solutions include financial services, energy and utilities, manufacturing, retail and wholesale, and software and internet services.
SD: What is the worst cyber threat today?
EA: People and users pose the greatest cyber risk today. It’s easier to trick someone into giving you the information you need vs. breaking into a system and circumventing controls to get it. In general, people are trusting so it’s easy to prey on them. Additionally, system users don’t always appreciate the risks they’re taking when handling data or collecting information. For example, it’s very simple to accidentally email out employee payroll information to a cached email address in your email client. Or maybe you want to test an application in the cloud, and you need some data to validate that it’s working. It’s easy to drop production/customer sensitive information where it shouldn’t be and have someone stumble across that temporary server that was never hardened. User mistakes and unintentional consequences from seemingly harmless decisions will always pose threats we have to manage.
SD: How is the cybersecurity landscape going to change over the next few years?
EA: The cybersecurity landscape is likely to shift due to two main factors: the increasing complexity of privacy rules and laws and cyber attacks with more catastrophic consequences.
In terms of privacy rules and laws, there will be an increased struggle for businesses to abide by the increasingly complex regulation and maintain a balance between security and privacy rights. We’re seeing a strong trend with a slew of privacy laws coming out like GDPR and CCPA that aim to put control of personal data back into the hands of individuals. We are likely to see more substantial punitive damages and penalties imposed on companies that are negligent in protecting data. These laws will continue to mature, become more stringent, and be more challenging to navigate.
On the other side of this equation, we’re going to see a battle between public health and the right to privacy. Take the COVID pandemic right now – contract tracing could be much more effective if we could track a person’s whereabouts, who they’ve been in contact with in the past 14 days, and where those additional contacts may have traveled. If we could then identify that person and all potentially affected people, we could curb COVID outbreaks much more quickly. While that sounds good in practice, there is the potential for unintended privacy implications that must be considered. There will most likely be a battle around privacy rights that will be much different in a post-COVID world.
In terms of cyber attacks, most of the public breaches and attacks experienced have been conducted for financial gain (e.g., ransomware and credit card theft), intellectual property/information gathering, or hacking for fun/notoriety. Eventually, we’re going to see the proliferation of technology (think IoT and connected everything) used as the vector for state-sponsored or terrorist attacks. Everything is connected and networked these days, and that will only continue to grow from phones and cars to medical equipment and massive operational control (OT) networks. We’re likely to see a cybersecurity attack be tied to a digital terrorist event and/or significant loss of life in our lifetime.
Source of Article