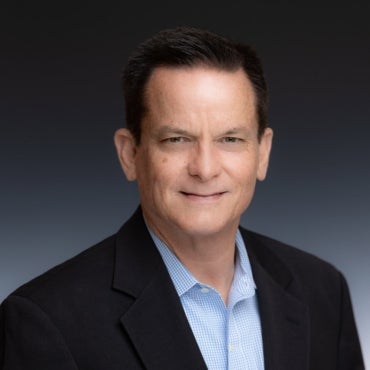
As an F-15 fighter pilot in the U.S. Air Force, William “Hutch” Hutchison flew high-stakes, train-to-failure exercises in aerial jousting of the type popularized by movies like “Top Gun.” After exiting the cockpit for good, he applied to cyberspace the principles of combat training he had learned flying in airspace by creating and leading numerous DoD cybersecurity IT training, certification, testing and assessment programs (Figure A).
Figure A
After the Air Force, Hutchison took a leadership role in the U.S. Cyber Command, where he oversaw the first joint, force-on-force tactical cyber training exercise Cyber Flag. He built a team that launched the first cyber adversary tactics office, founded the first joint cyber-focused tabletop exercise and established an inaugural cybersecurity team certification. With elements from MIT’s Lincoln Laboratory along with Johns Hopkins University Applied Physics Lab, Hutchison and his team also developed the first-ever test series for the DoD.
SEE: Cybersecurity adoption hampered by shortage of skills and poor product integration (TechRepublic)
Hutchison’s next move was to the private sector, where he and members of his Cyber Command team co-founded the cyber range company SimSpace in 2015. Using digital twins, bots and other automation — not to mention squads of human white hat operators — SimSpace has been running cyber ranges worldwide for the government, military and global cyber defense, plus private sector industries like energy, insurance and finance.
The company, which says it can simulate three years of unpredictable live-fire attacks in 24 hours, partners with numerous security platforms including Google Mandiant, CrowdStrike, SentinelOne and Microsoft.
TechRepublic Q&A with SimSpace CEO William Hutchison
Grounded: Putting red team skirmishes in cyberspace
Q: How would you characterize the range of SimSpace’s deployment?
A: The vast majority of our work is with enterprise companies, militaries and governments. We work with the U.S. Cyber Command, the FBI and other elements within the U.S. government, for instance.
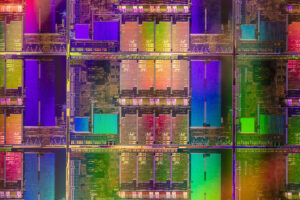
One of the interesting developments recently was our expansion globally into Japan, so we are working with the equivalent of their DHS and FBI there. What we’ve found is that from there, there’s a close coupling with their ministry of defense, banks, telecoms and transportation, and there is a strong pull from eastern Europe because of geopolitical circumstances (Figure B).
Figure B

Q: It’s axiomatic that there’s a massive cybersecurity talent shortfall — some 3.4 million empty seats if you subscribe to (ISC)² 2022 Cybersecurity Workforce Study. How important are cyber ranges to helping to cultivate and retain talent?
A: When we work with our commercial partners, we find that there is a big, big gap not only in terms of sheer numbers, but in the number of qualified operators, which is even a smaller group. What was really revealing to me was that the top banks in the U.S. get to cherry-pick the best and brightest, and even though a lot of these people have ten years experience, they have not conducted cybersecurity exercises: The cybersecurity equivalent of hand-to-hand combat.
SEE: Recent 2022 cyberattacks presage a rocky 2023 (TechRepublic)
Historically, the training curriculum was just not suited to the needs required, so as a company we have led with the ability to focus on team-level performance, organizational risk and how to test security stacks. We have invested for a couple of years on structured, prebuilt, training-focused content, and we challenge teams by doing things like taking away security tools — SIEM tools, endpoint protection, something they are relying on — because a determined adversary will disable these, and now your job is to go to Plan B.
Q: Do you have a sense of how many companies are conducting cyber ranges?
A: First, I think we are the only ones who can create something of this complexity. Other cyber range vendors focus on the individual — a couple of virtual machines to support a structured curriculum — but without being able to replicate production with their security tools and take the time to configure them as they have in production.
The short answer is there may be some penetration testing and a little red teaming of a network, but they can’t go “gloves off,” because you have to worry about inadvertently breaking something by attempting something unorthodox that, in the course of training, could cause something to happen of an operational concern. What’s helpful about the range is the ability to do it safely, offline.
Applying digital twins to keep exercise safely out of the production space
Q: A big part of this for SimSpace is the use of digital twins. What does that mean in a cyber range context?
A: We are a little different from the traditional digital twin, and there’s a little confusion about the concept. There are the IT components, whether endpoints or network devices, and that’s one thing, but one of the secret sauces of our platform is the ability to generate traffic, not just replay it, by putting bots in each host, each given a persona to act like a manager or administrative assistant.
For example, they all have unique web surfing behaviors, and will do things like build Excel spreadsheets, Word documents, attach them to emails and send them back and forth to one another. They have diurnal patterns and goals and tactics. It’s that traffic that is the life blood of your network — what you would find in the real world.
The adversarial signal is what you have to delineate from all that noise, so when we talk about a digital twin, it’s not just virtualizing the network. For the past eight years, we have worked hard to automate some of the things that go to accelerating the planning, executing and reporting.
Q: To the extent that doing cyber security is, in effect, trying to patch a tire while you are riding the bike — with developments around malware as a service and new kinds of vulnerability around things like automation — how do you innovate the cyber range to keep pace with tools at the disposal of bad actors?
A: It’s a challenge. On the training front, not only is the adversary changing, but the corresponding security response and underlying IT infrastructure is changing, and that could very well change the IT security solution or the adversarial threat presentation.
I think that one company alone can’t address all of these threats. There’s a way to bring together a variety of solutions on the training floor. In terms of keeping up with the threats — let’s say the automated threat framework — we have a dedicated team, but I’ll be first to tell you that, yes, it is reactionary: We are trying within a week to get something out that shows both the offensive side and then a good set of remediation steps.
Q: How do you prepare for future threats you may not know exist?
A: One of the use cases of our platform, which is one of the really great things about a range, is that it allows you to do hypothesis testing: You can test the future state of your network.
In other words, one of the advantages of a range is that you can be proactive in the sense of understanding what your future state risks would be and work with the right R&D entities to keep ahead of some of the expected threats.
Q: Where does the cyber range fit into the larger acquisition process for talent?
A: If you admit that with enterprise level organizations — and you can throw in governments, as well — proper IT security requires team level, even multiple team-level responses, then the sequence of preparation for IT security response, strictly on the people side would be:
- Identify the right candidates.
- Train them.
- Certify their performance and move them into a team.
- Do exactly the same thing at the team level: Train, certify or accredit the team.
- Train them on cyber ranges.
This is a continuous cycle on an annual basis at the teams level: Getting the lead out, getting refreshed. We own that team-level training and assessment, as well as mission rehearsal on the individual and team side as well. A continuous improvement cycle for individual and corresponding teams.
Staying versatile and retaining talent
Q: In terms of the threat landscape — 5G telecoms, for example — from your point of view, do you see any special areas where you think there will be a need to focus on that, whether it be cyber range or any other defensive frameworks that are available?
A: There’s always going to be a new wrinkle. The last one was migration of traditional data to the cloud. Most recently, with the pandemic, the borders of a company’s networks expanded to employees’ homes, so the IT landscape will keep evolving.
A prudent approach to cybersecurity is to assume there is going to be a breach. What we work on is identifying the behaviors as quickly as possible and then effective responses.
Q: Any thoughts on how the use of cyber ranges and challenging teams can actually help retain talent?
A: You know, it isn’t always obvious that teams want to be challenged. People tend to think they are very good at their job.
I’ll tell you a story: In year one, when we worked with a major bank, I didn’t know if this whole military thing would work, and we did a two week engagement. The first week, the blue team wasn’t happy. So what we did was bring the red team from behind the curtain and had them sit with the blue team, and once the blue team figured out what the exploits were, it went from being a very negative, frustrating experience for them to something very, very positive, from which they got a lot of learning.
So, yes, I do think there are teams out there waiting to be challenged, who love their mission, and I think you could improve retention in hiring and keep the best with challenging preparatory activities. Frankly, it’s also a great crucible for leadership training.
Conclusion
Cyber ranges are not one and done — it’s continuous training. If you are seeking ongoing, lifetime cybersecurity training and certification, consider Infosec4TC with Unlimited Access to Self-Paced Courses on GSEC, CISSP & More. Learn more here.
Source of Article