Published on: May 9, 2024
On May 2, the US Federal Bureau of Investigation (FBI), the National Security Agency (NSA), and Department of State issued a joint cybersecurity advisory warning email recipients that APT43, a cyber threat actor run by North Korean military intelligence, is using a vulnerability in email configurations to target organizations for intelligence exploitation.
The US Joint Cybersecurity Agency, which the above agencies belong to, has noticed an uptick in spear-phishing emails — targeting specific individuals with messages that appear to come from trusted sources — against journalists, academics, researchers, policy analysts, and others who may have information of interest to the North Korean government.
The spear-phishing campaign is designed “to provide stolen data and valuable geopolitical insight to the North Korean regime by compromising policy analysts and other experts,” according to the advisory. The email senders pose as legitimate members of the East Asian and Korean policy community in an attempt to get recipients to click on links or download attachments in the emails. These actions usually give the senders unfettered access to not only the recipients’ communications but everything on the organization’s email servers.
The APT43 group, also known as Kimsuky, is using a common vulnerability in email configurations to send email that appears to come from legitimate domains familiar to those targeted. The threat actors use absent DNS Domain-based Message Authentication,
Reporting and Conformance (DMARC) record policies in an organization’s email setup to ensure their malicious emails get through to the recipients.
Normally, DMARC record policies reject mass emails, spam, and email whose sources can’t be verified. DMARC ensures that received emails are coming from the domain that they say they’re coming from. If they can’t be verified, the email is not delivered, or it’s returned to the sender unopened. However, if the DMARC record is left blank, unverified email can get through, and spear-phishing email from North Korea can get through unnoticed until it’s too late.
DMARC record policies are important enough that Google’s Gmail service has started using them to filter out spam from users’ inboxes. “Google has recently implemented new email authentication rules that will see non-authenticated messages from bulk senders to Gmail addresses returned unopened… to reduce the amount of spam and, in turn, reduce the potential for that spam to be carrying malicious content to Gmail users,” according to Forbes cybersecurity experts.
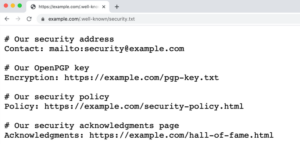
The US Joint Cybersecurity Agency strongly urges all email administrators, but especially those in the targeted sectors, to immediately populate the DMARC fields in their email configurations. It’s a matter of entering just one or two lines of code (the instructions can be found in the advisory here) — a quick fix that can prevent their organizations and employees from being exploited by North Korean intelligence.
Source of Article