Published on: February 27, 2023 
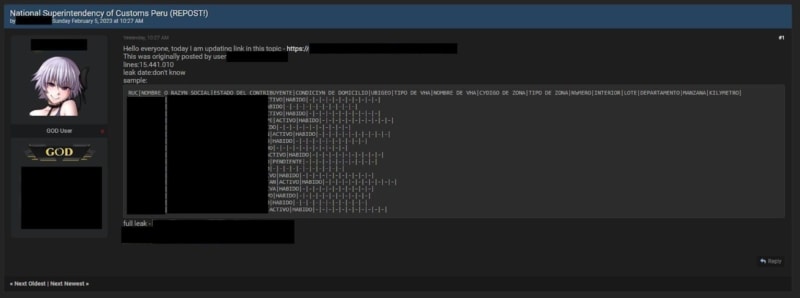
The SafetyDetectives cybersecurity team recently discovered a database shared on a clear web forum for free, presumably belonging to the Peruvian governmental entity, SUNAT on February 5th, 2023.
The database consists of approximately 1.2GB worth of unencrypted data, containing 15,441,010 lines in a .TXT document, and can be downloaded by anyone with access to the forum post.
The source of the database or how it was obtained is unknown, but this is not the first time it was shared as it is an update from a similar post made in December 2022, according to the author of the post.
The exact number of individuals affected by the sharing of the SUNAT database on the forum is unknown. However, according to the author the database contains 15,441,010 lines of information, potentially exposing up to 15 million (estimated) Peruvian citizens (each line of information appears to relate to a single individual, as noted from the forum post in question).
Who was affected?
The governmental entity affected is the “Superintendencia Nacional de Aduanas y de Administración Tributaria” (the National Superintendency of Customs and Tax Administration), more commonly abbreviated as “SUNAT”, which is the national tax administration agency of Peru. It is responsible for collecting and managing tax revenues, as well as customs duties, for the Peruvian government. SUNAT plays a crucial role in the country’s economy and is responsible for ensuring compliance with tax laws and regulations.
What was exposed?
The following list is an example of the types of data that was exposed in the sample shared via the forum post:
- RUC (tax identification number)
- Nombre o razón social (name or business name)
- Estado del contribuyente (taxpayer status)
- Condición de domicilio (tax domicile condition)
Our team of researchers only reviewed a sample of the SUNAT database that was shared via the forum, and did not access the full database for ethical reasons. The data listed above, including RUC, name/business name, taxpayer status, and tax domicile condition, was the only information observed in the sample. There may potentially be other types of information present in the full database, as some fields appear blank in the sample shared in the forum post.
Understanding a breach and its potential impact takes careful attention and time. We strive to publish accurate and trustworthy reports, to ensure our readers understand the impact of the data exposures highlighted.
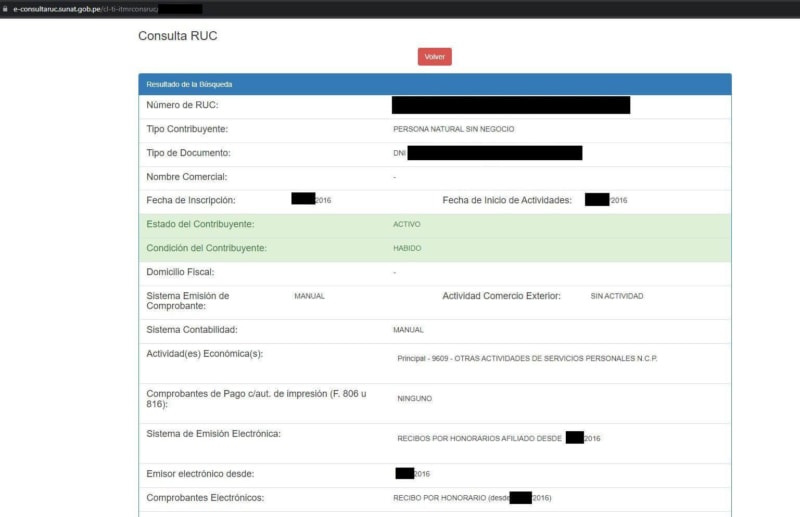
On that note, we place great importance on being thorough and making sure our findings are valid and accurate as far as reasonably possible. Our team sought to verify the authenticity of the data by cross-checking the validity of a RUC found in the sample through a separate Peruvian government website, which provides for the verification of taxpayer status in Peru. The data in the exposed database was confirmed to be real data belonging to Peruvian tax residents, and not “dummy” data.
This verification process, however, could also expose sensitive information such as an individual’s national identity registration number (DNI), which could be used for fraudulent purposes. The fact that this information can be easily accessed highlights the dangers arising from the exposure of the SUNAT database.
Our team contacted the Peruvian authorities on February 13, 2023, and alerted them of the data being shared online. At the time of writing, we haven’t received any response from SUNAT.
We do not know, or have a way to determine how this information was leaked, as there are many ways in which this information could have been exposed. Additionally, we cannot determine whether anyone else accessed the data while it was exposed.
Potential impact
The exposure of the SUNAT database has the potential to cause significant harm to Peruvian citizens. The data contained in the database consists of highly sensitive information, including tax identification numbers, names/business names, taxpayer status, and tax domicile condition.
Such data may potentially be used on other governmental/private websites as a unique identifier, in order to obtain and mine more detailed information from an exposed user. The exposed information could fuel further fraudulent activities, allowing malicious actors to possibly steal identities, take out loans, and engage in other forms of financial fraud.
In addition, the exposure of this information can also result in a loss of privacy and a loss of trust in the government’s ability to protect citizens’ personal data. The potential impact of this data breach is significant and can have long-lasting consequences for Peruvian citizens.
What can you do if you think you could be affected by the leak
Individuals who believe they may have been affected by the exposure of the data, can take several steps to protect themselves:
- Monitor their financial statements regularly for any suspicious activity.
- Contact their bank and financial institutions to report any suspicious activity and request fraud alerts.
- Report any suspected identity theft to the appropriate authorities.
By taking these proactive steps, individuals can minimize the potential impact of the data leak and reduce the risk of identity theft or other forms of fraud.
About us
SafetyDetectives tests, compares, and reviews antivirus software, password managers, parental control apps, and virtual private networks (VPNs) using a robust testing methodology.
The SafetyDetectives research lab is a pro bono service that aims to help the online community defend itself against cyber threats. We aim to help the online community defend itself against modern-day cyberattackers while educating organizations on how to protect their users’ data.
Find out more about what constitutes cybercrime, the best tips to prevent phishing attacks, and how to avoid ransomware by following SafetyDetectives’ blog and our latest news.
Source of Article